How XTRABYTES™ Is Preparing To Be Quantum-Resistant
XTRABYTES™ has adopted several solutions to counter it as a potential threat. We believe these solutions will prepare us for the quantum age and enable us to guarantee a safe and trustworthy network.

– Encryption flexibility as a quantum-resistant approach
Aside from implementing the latest cryptographic schemes, we’ve also created a network that enables us to quickly implement such schemes when needed. This flexibility will allow our network to easily stay ahead of any new quantum computing developments.
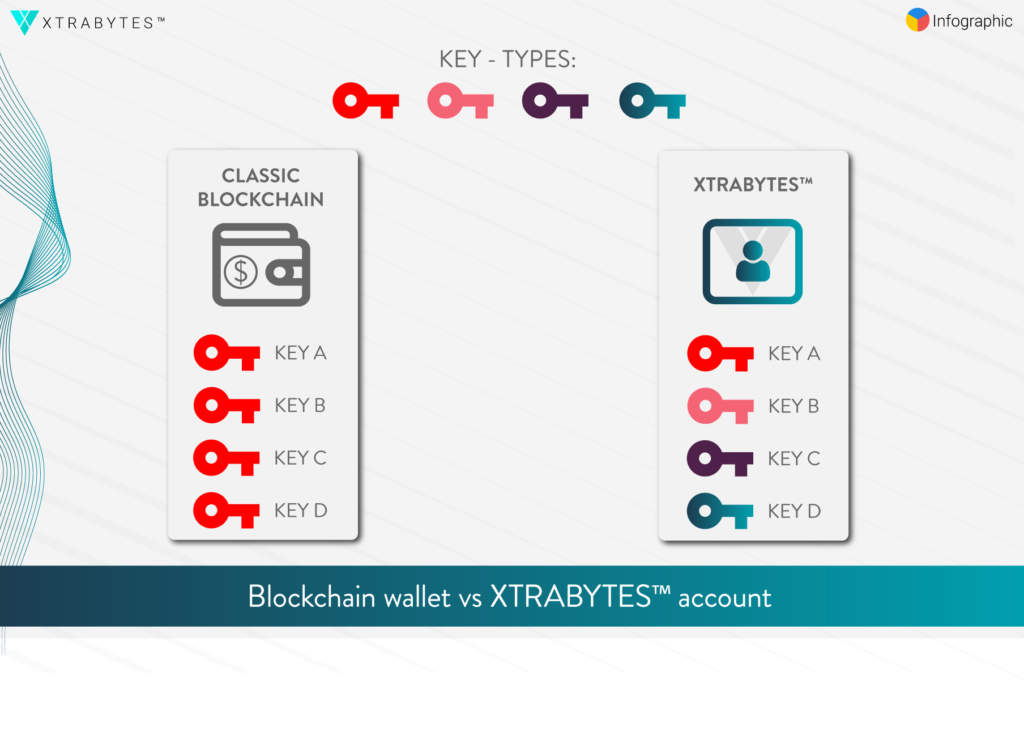
Moreover, while nearly all cryptocurrencies rely on a wallet that holds one type of key (all of which are used in the same encryption scheme), the XTRABYTES™ network will employ accounts that can hold a variety of encryption keys. By doing so, we’re able to allow each application/service to select which encryption scheme they would like to use.
Encryption schemes with asymmetric keys, which could serve as a replacement for RSA or ECC key pairs, and which are considered quantum-resistant, already exist. However, these schemes (among them the Lamport Signature scheme, Ring Learning With Errors Signature scheme, and the Rainbow Signature scheme) retain some limitations and/or require more testing. Nonetheless, our team is keeping a close eye on their development, as our network will want to readily accept them once they have been thoroughly tested.
Amazingly, other blockchains rely on only one encryption scheme to protect their entire network. This inevitably exposes the network if the relied-upon encryption scheme is compromised
In contrast, the XTRABYTES™ network will employ a variety of encryption schemes for our various network components. By ensuring that our network retains diverse and flexible security, we aim to ensure its superiority over networks with singular encryption schemes. And by preventing one encryption scheme from becoming a single point of failure, this approach improves the decentralized nature of our network.

When it comes to encryption schemes with symmetric keys, our XCITE™ client currently incorporates AES-256 to encrypt all account data. This encryption scheme is still considered quantum-resistant despite recent advances in quantum computing.
We selected this particular encryption scheme for XCITE™ as it is still regarded as one of the top encryption schemes that use symmetric keys. Not incidentally, it’s frequently employed worldwide by private companies and public entities alike.
In June 2003, the U.S. Government announced that AES could be used to protect classified information: “The design and strength of all key lengths of the AES algorithm (i.e., 128, 192 and 256) are sufficient to protect classified information up to the SECRET level. TOP SECRET information will require the use of either the 192 or 256 key lengths. ” The U.S. Government still uses the AES encryption scheme today
Nonetheless, we do not consider ourselves bound to any one particular encryption scheme. And should the need arise, we have the capacity to upgrade to a new and even more secure encryption scheme. Individuals seeking to learn more about the encryption schemes employed by our network will be able to do so by taking courses at The XTRABYTES Academy.
– No mining requirements
For starters, XTRABYTES™ does not require mining. When a STATIC™ node provides continuity for the network, that STATIC™ node is not rewarded with new coins (more about this in one of our upcoming articles). Furthermore, when it comes to Proof of-Signature (PoSign™), using a quantum computer to run a STATIC™ node will not provide a node owner with an unfair advantage over other node owners.
Although our PoSign™ consensus algorithm relies on pseudo-random selection as well, the STATIC™ node in charge of providing continuity for the network only has limited control over the data that is included.
Instead, PoSign™ is built to maximize the number of data transactions, as all the STATIC nodes seek to ensure that a maximum of data transactions is included. This leaves the STATIC™ node in charge no room to decide which data transaction data to use and which to ignore, eliminating any threat that the network could be hijacked in the process.
Likewise, the STATIC node in charge of providing continuity will be unable to insert additional data transactions, even if they are valid data transactions (as it would go against the consensus rules). We’re able to achieve this qualification by incorporating our network with 3 different network levels, in which each level is configured to play a specific role within the network.
This setup also guarantees that everyone follows the consensus rules, penalizing any attempt to bypass these rules with reduced trustability and/or exclusion within the network.
– Tiered network levels as quantum-resistant security
In order to counter any hash collision exploits, our unique STATIC node network works in tandem with our PoSign algorithm. For a hash collision to lead to an exploit, our patented technology requires collisions to occur on different network levels simultaneously. In addition, these simultaneous collisions would need to provide usable data on all network levels for any attempted attack to be successful.
Since each node level has its own role to play in the PoSign process, the data being employed on any one level must be specifically validated. This validation is based on a combination of different hashing techniques and signature schemes, thus ensuring that no one has tampered with the data.
The STATIC nodes for any one level have no control over which data needs to pass this validation process. They cannot exclude any data without providing proof that the excluded data is in violation of the consensus rules, nor can they insert any additional data that would otherwise be provided by a STATIC node on a different level.
Ultimately, any attempt to deviate from the consensus protocol will be visible by everyone in the network. In addition, such a violation would result in the exclusion of the data that triggered the violation. Indeed, it would also reduce the trustworthiness of a node owner seeking to deviate from the consensus protocol, possibly leading to the revocation of his/her access rights (especially if it occurred more than once).
PoSign dramatically reduces the possibility that a hash collision will result in an exploit. Indeed, the probability that such a collision could produce alternative data that is not in violation of the consensus rules, and also passes different levels of validation, can be considered a statistical impossibility. Consequently, we consider PoSign to be remarkably resistant to any form of hash collision exploit.
Providing a Quantum-Resistant Future
By combining cryptographic agility with our revolutionary PoSign™ technology, we have created a network that is ready for the quantum computing age. In the meantime, we intend to further develop and improve our quantum-resistant network in order to keep up with any challenges that it might face in the future.
This makes XTRABYTES™ the only network that actively avoids hash collision exploits, prevents the possibility of quantum mining and is flexible enough to adapt to new and more secure encryption schemes. Our network will even decentralize the encryption that we implement, thus providing superior protection against any similar centralized decryption approach.



